OpenClaw and Anthropic: Account Suspension Fallout Explained
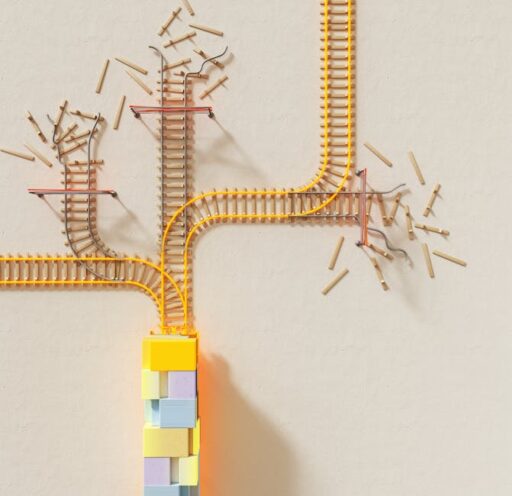
A high-profile developer briefly had an account suspended after running OpenClaw with Anthropic models, then saw the account reinstated within hours. The incident exposed tensions around third-party agent tooling, new usage-based pricing for “claws,” and the operational realities of testing cross-provider compatibility. This article unpacks the timeline, technical issues, policy rationale, and practical steps developers and organizations should take to stay resilient.
What happened with OpenClaw and Anthropic?
In short: a prominent OpenClaw developer reported a temporary account suspension after interacting with Anthropic’s platform while testing agent integrations. The account was restored a few hours later, but the episode sparked a broader conversation about how model providers manage third-party agent tooling, enforce new pricing policies, and communicate with developers.
Timeline summary
The core sequence was straightforward:
- The developer used OpenClaw to interact with an Anthropic model as part of compatibility testing.
- Anthropic flagged the activity as “suspicious” and suspended the account.
- The suspension was reversed within hours after public attention and internal review.
Although the immediate problem resolved quickly, the episode revealed deeper friction points: how providers detect unusual usage patterns, how pricing and subscription models handle continuous or agentic workloads, and how public forums amplify developer concerns.
Why did Anthropic change OpenClaw pricing and enforcement?
Anthropic introduced a policy change that moves third-party harnesses like OpenClaw onto consumption-based billing via the Claude API, arguing that subscription plans were not designed for the sustained or atypical usage patterns produced by agentic tools. Key reasons cited by providers for such changes typically include:
- Agents run persistent reasoning loops, retry tasks, or orchestrate external tools — creating steady or bursty compute consumption that subscriptions may not cover.
- Third-party harnesses can amplify API calls and stateful sessions that require different telemetry and rate-limiting than interactive chat usage.
- Providers aim to discourage abusive automated behavior and ensure predictable infrastructure cost allocation across user classes.
From a product perspective, placing agent-style usage on a pay-for-consumption model is defensible. It aligns costs with resource consumption and gives providers a signal to optimize for different workload patterns. But it also introduces friction for open-source tooling and for developers who need to test compatibility across models.
How did the developer respond and why does it matter?
The developer emphasized two parallel roles: maintaining an open-source project that aims to work across model providers, and holding a separate role at a major model company focused on strategy. He said testing other providers is essential to keep OpenClaw reliable for users who prefer non-default models, and that he had been following the new pricing rules. The suspension despite apparent compliance raised concerns about transparency, false positives, and unintended lock-in dynamics.
This incident matters because:
- It highlights the tension between provider safeguards and developer workflows.
- It underscores the importance of clear communication around enforcement triggers.
- It demonstrates the community impact when moderation or account actions affect widely used open-source tooling.
What are the technical drivers behind enforcement?
Providers use automated systems to identify unusual activity. For agentic tools, signals that often trip enforcement systems include long-lived sessions, rapid automated retries, repeated orchestration of external services, and atypical traffic patterns that deviate from conversational usage. Technical drivers include:
- Session persistence and streaming tokens that keep memory alive across tasks.
- Looping behavior and automatic retries that magnify API call counts.
- Tooling integrations that create spike patterns in requests to external endpoints.
These behaviors are not inherently malicious, but they require different monitoring and billing logic compared with human-in-the-loop chat traffic.
What does this mean for developers and organizations?
The broader implications affect developer practices, open-source maintainers, and enterprise buyers:
Developer impact
Maintainers of agent frameworks must adapt to variable billing models and implement safeguards to avoid accidental overuse. Testing across multiple providers remains essential to prevent regressions for users who choose alternate models.
Open-source and interoperability
Policy changes that move agent workloads to consumption billing create an operational cost for open-source projects. This can limit the ability of small teams to provide free, cross-provider compatibility unless providers create developer-friendly allowances or academic tiers.
Enterprise procurement
Enterprises should assess how model-provider billing will affect productionized agents, especially when agents run continuous tasks or integrate with many services. Budgeting and testing strategies should account for consumption spikes and sustained workloads.
Best practices: How to reduce risk and maintain compatibility
To reduce the chance of account suspension or unexpected costs, follow these recommendations:
- Instrument usage: Track and report the number of calls, session durations, and token consumption per test run so you can prove compliance when a provider raises concerns.
- Throttle and backoff: Implement exponential backoff, rate limiting, and safeguards to avoid retry storms.
- Isolate test environments: Use dedicated developer API keys tied to billing accounts explicitly designated for agentic workloads.
- Communicate proactively: If you run large-scale or continuous tests, notify provider support teams in advance and request guidance on acceptable behavior and billing expectations.
- Plan for multi-provider testing: Create scripts and CI checks that simulate typical user loads and include cost estimates so maintainers or employers can anticipate billing changes.
How should model providers improve transparency and developer experience?
Providers can take concrete steps to prevent confusion and surface fewer false positives:
- Publish explicit detection heuristics and examples of activity that triggers enforcement.
- Offer developer tiers or credits for open-source maintainers who need to run cross-provider compatibility tests.
- Create clearer billing categories that distinguish interactive chat from continuous agent processing.
- Provide a fast, human-reviewed appeals channel for account actions affecting well-known projects.
When providers and developer communities collaborate on these operational details, the ecosystem benefits from both safer platforms and robust open-source tooling.
Related coverage and deeper context
These themes are consistent with broader industry patterns: selective feature rollouts, governance trade-offs, and compute billing shifts. For more on selective rollouts and release strategies at AI companies, see Anthropic Mythos Rollout: Why Selective Releases Matter. For a deeper look at model security trade-offs and risk assessments, refer to Anthropic Mythos Model Preview: Security Uses & Risks. And for how company strategy and leadership moves shape the market, review our piece on OpenAI Leadership Changes: Market Impact & Next Steps 2026.
Frequently asked question: Can a compliant developer be suspended by mistake?
Yes. Automated enforcement systems can generate false positives when traffic patterns resemble abusive behavior even if the intent is legitimate. Common triggers include long-lived sessions, rapid automated retries, or unusual token consumption. Developers can mitigate this risk by following the best practices above and by keeping clear logs and billing records to expedite appeals and reinstatement.
Practical checklist before running agentic tests
Use this quick checklist to prepare for safe and predictable testing:
- Confirm billing tier supports long-running or high-volume workloads.
- Allocate a dedicated API key and billing account for agent tests.
- Implement rate limiting and retry guardrails.
- Instrument telemetry for token, call, and session metrics.
- Notify provider support if running large or continuous experiments.
Conclusion
The OpenClaw–Anthropic suspension and quick reinstatement underline a modern reality: providers are updating pricing and enforcement to reflect new agent-driven workloads, and sometimes enforcement systems misclassify benign developer activity. The fix is twofold. Providers must improve transparency, billing categories, and developer support. Developers must adopt safer testing practices, robust instrumentation, and proactive communication to avoid costly interruptions.
Next steps for developers
If you maintain or rely on agent tooling, audit your test pipelines today. Ensure you have observability on session lifetimes and token usage, and reach out to providers proactively when you plan sustained tests. These small changes will reduce the risk of being flagged and will make cross-provider support more durable.
Call to action
Stay informed and protect your integrations: subscribe to Artificial Intel News for ongoing analysis of platform policy changes, implementation guides, and developer playbooks that keep agentic AI systems robust across providers.