AI Content Moderation: Policy-as-Code for Real-Time Safety
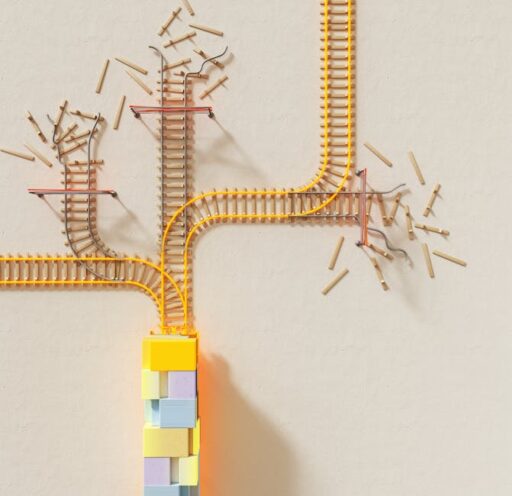
As generative AI and chatbots become core components of consumer and developer products, platforms face escalating risks from harmful, disallowed, or otherwise unsafe content. Traditional workflows—bulk human review, long policy documents, and after-the-fact enforcement—no longer scale. Developers and trust-and-safety teams now need a different architecture: real-time, codified policies that integrate directly into content pipelines.
What is policy-as-code and how does it stop harmful content in real time?
Policy-as-code converts written guidelines into executable, versioned logic that runs at runtime. Instead of expecting human reviewers to memorize and apply long, often machine-translated manuals under time pressure, platforms can evaluate content against an up-to-date rule set in milliseconds. The result is deterministic, auditable enforcement that can throttle, block, flag, or steer interactions before harm proliferates.
Key characteristics of policy-as-code systems
- Executable rules: Policies expressed as code or logic that can be run automatically.
- Runtime evaluation: Content is evaluated at the moment it is generated or shared, not days later.
- Actionable outputs: The system returns clear actions (block, slow, escalate, steer) with context for human review.
- Auditability and versioning: Every rule change is tracked so decisions are explainable and reversible.
Converting policies into code doesn’t remove human oversight; it repositions human reviewers to handle edge cases and complex appeals while automation handles scale and speed.
Why the old model fails with modern AI
Historically, platforms relied on human moderators to apply large policy manuals under tight time constraints. Reviewers often had seconds per item and imperfect translations of policy text. Even with the best intent, accuracy was inconsistent and enforcement delayed—allowing harm to spread before a decision arrived.
The arrival of powerful LLMs and multimodal generators has magnified the problem. Bad actors can iterate quickly, find policy blind spots, and craft content that bypasses static filters. Meanwhile, chatbots can produce unsafe outputs in conversational contexts, and image models can generate harmful imagery faster than humans can react. This combination creates three pressing needs:
- Speed: Decisions must happen in milliseconds to keep content from going viral.
- Consistency: Rules must apply uniformly across languages, formats, and contexts.
- Adaptability: Policies must update as adversaries evolve and new harms appear.
How modern moderation stacks work
Leading approaches split responsibilities across layers that together deliver scale and nuance:
- Edge filters: Low-latency heuristics and fast classifiers that catch straightforward violations.
- Runtime policy engine: A policy-as-code core that checks content against codified rules and returns structured actions.
- LLM contextual evaluators: Models trained to interpret policy documents and provide risk scores or suggested actions in human-readable form.
- Human review and appeals: Cases flagged as ambiguous or high-risk are routed to trained teams with full context and audit trails.
This layered design balances speed and precision: trivial cases are handled instantly, while nuanced scenarios escalate for human judgment.
How can platforms implement policy-as-code today?
Implementing policy-as-code is both technical and organizational. Here are practical steps teams can take:
- Inventory policies: Convert written rules into discrete decision points (e.g., “sexual content”, “self-harm encouragement”, “minor exploitation”).
- Define actions: For each decision point, define precise actions: allow, slow distribution, block, label, or escalate for review.
- Build a runtime engine: Use a rules engine or executable workflow layer that accepts content and returns structured responses within strict latency targets.
- Integrate contextual LLMs: Where nuance matters, employ models trained to parse policy text and provide rationale or risk scoring.
- Instrument audibility: Keep logs, rule versions, model outputs, and human decisions for compliance and continuous improvement.
- Test adversarially: Run red-team exercises to simulate how bad actors might try to bypass rules, and iterate policies accordingly.
These steps turn safety from a reactive afterthought into an integrated product capability. In many cases, teams report substantial improvements in detection accuracy and incident response times when policy-as-code architectures are properly implemented.
What does real-time enforcement enable?
Real-time enforcement lets platforms do more than just block content. It enables a spectrum of responses that preserve user experience while reducing harm:
- Soft throttles: Slow or limit distribution while a piece of content undergoes deeper review.
- Contextual steering: Intervene in conversations to nudge a model or user toward safer responses rather than bluntly refusing.
- Graduated penalties: Apply warnings, temporary limits, or full blocks based on risk and history.
- Proactive labeling: Attach safety labels or content warnings when automated checks indicate potential risk.
These nuanced actions preserve user utility and reduce false positives compared with one-size-fits-all blocking.
Iterative steering: a new moderation tactic
One of the most promising tactics emerging from runtime systems is “iterative steering.” Instead of issuing an abrupt refusal when a chatbot or generator nears harmful territory, iterative steering intercepts the flow, modifies or augments the prompt, and guides the agent toward constructive responses. This approach uses prompt transformation, constraint enforcement, and empathy-focused rewrites to achieve several outcomes:
- Reduce user frustration by providing a helpful alternative
- Lower the likelihood of evasion or adversarial retries
- Preserve engagement while addressing safety concerns
Iterative steering requires tight collaboration between policy engines, model prompts, and evaluation metrics. When done well, it can transform safety from a liability into a product differentiator.
How accurate are LLM-powered moderation layers?
Accuracy varies by vertical and deployment, but modern LLM-aware systems can substantially improve detection rates compared with ad-hoc manual review. Some deployments report order-of-magnitude gains in precision and recall when LLM-based evaluators are combined with policy-as-code and human-in-the-loop workflows. Crucially, these systems are most effective when rules are iterated continuously against real-world data and adversarial inputs.
Which verticals benefit most?
Policy-as-code and real-time moderation are particularly valuable for:
- Social and dating platforms with user-generated content
- AI companion and character platforms with conversational agents
- Image and video generation services that produce potentially explicit or misleading media
Platforms in these categories combine high user engagement, fast content creation, and significant exposure risk—making real-time safety an operational necessity.
How do third-party moderation layers fit in?
Some companies choose to build their entire safety stack in-house; others adopt third-party runtime safety layers that sit between users and content generators. Third-party systems can offer several advantages:
- Specialized expertise in encoding complex policies into executable logic
- Shared threat intelligence and rule libraries across customers
- Faster time-to-market for safety features like throttling and steering
Using an external safety layer does not absolve platforms of responsibility; rather, it augments internal capabilities and offers redundancy when internal guardrails are still maturing.
What operational metrics should teams track?
To measure the effectiveness of policy-as-code implementations, track both safety outcomes and user experience metrics. Key indicators include:
- False positive and false negative rates by violation category
- Average decision latency (ms)
- Volume of automated actions vs. escalations to humans
- Appeal and overturn rates for human-review decisions
- Incidents avoided (e.g., harmful content removed before widespread distribution)
Combining quantitative metrics with qualitative post-incident reviews creates a feedback loop that improves rule quality and model calibration.
How does this relate to on-device or edge AI?
Edge and on-device models reduce latency and preserve privacy but present trade-offs in compute and model complexity. For certain use cases, running lightweight safety checks on-device—paired with a centralized policy engine—can deliver low-latency protections while minimizing data exfiltration. For a deeper look at edge and on-device AI strategies, see our coverage on On-Device AI Models.
How does this connect to broader AI safety and governance?
Policy-as-code is one operational building block in a larger governance ecosystem that includes legal compliance, transparent reporting, red-team audits, and cross-industry standards. For context on legal and reputational pressures facing AI developers, consult our analysis of AI chatbot safety and regulatory debates in articles like AI Chatbot Safety: What the Gemini Lawsuit Teaches and AI Chatbots and Violence: Rising Risks and Safeguards.
Checklist: Building a practical policy-as-code program
Use this short checklist as an operational starter kit:
- Map policy to decision points and actions
- Set strict latency budgets for runtime evaluations
- Integrate LLM evaluators for context-rich cases
- Design graduated, explainable actions (slow, label, block, escalate)
- Implement robust logging, versioning, and audit trails
- Practice adversarial testing and continuous iteration
Conclusion: Safety as a product advantage
Turning policy into code and enforcing it at runtime changes the safety equation. Platforms gain deterministic enforcement, faster incident response, and the ability to embed safety into the product experience rather than treating it as a downstream cost. By pairing policy-as-code with LLM-aware evaluators, iterative steering, and rigorous human oversight, companies can reduce harm, lower legal risk, and—importantly—differentiate their products on the basis of trustworthy user experiences.
If your team is building or evaluating moderation infrastructure, prioritize measurable latency targets, invest in auditability, and run adversarial scenarios frequently. As adversaries and models evolve, the only reliable strategy is continuous iteration backed by clear, executable rules.
Take action
Want to stay ahead on AI safety and moderation best practices? Subscribe to our newsletter for deep dives, case studies, and implementation guides. If you’re evaluating policy-as-code or need a second opinion on runtime safety, reach out to our editorial team for recommended reads and expert connections.